As cybersecurity becomes a mainstream business risk, boards are coming under increasing pressure from customers, regulators, investors and the government to understand and oversee potential breaches effectively. Concern grows as the frequency and sophistication of high-profile cyber-attacks rise across industries.
In September, British Airways revealed that hackers had stolen the personal and financial data of 380,000 customers from its mobile app and website a few weeks earlier. Faced with customer anger, the airline had to promise to compensate passengers whose information had been stolen.
Tech giants have also been at fault over failure to protect user data. Google+ shut down its social media network in October, following its non-disclosure of a user data leak. At the end of September, Facebook revealed that hackers had accessed the data of 50 million users’ accounts, including those of its CEO Mark Zuckerberg and COO Sheryl Sandberg. The social network group is still under scrutiny after an earlier data protection leak, where research firm Cambridge Analytica obtained the data of 87 million Facebook users.
Failure to protect personal information and to be transparent about how the data is harvested by others shocked social media users, sent Facebook’s share price plummeting and incurred a £500,000 fine from the UK watchdog.
Companies also face cybercrime attacks from hostile states. In June 2017, Reckitt Benckiser, Moller-Maersk and FedEx suffered a NotPetya ransomware attack, which disrupted their operations and cost each company millions of dollars. Russia has been accused of the attack. A month earlier WannaCry ransomware, perpetrated by North Korea, disabled the operations of thousands of companies in about 150 countries, and also UK hospitals.
—Ciaran Martin, NCSC
At a September CBI cybersecurity conference, Ciaran Martin, CEO of the National Cyber Security Centre (NCSC), stressed the urgency of cyber-threats and called on boards to become more cyber-literate to make company defences stronger.
“This means closing the knowledge gap between the board and the technical team … so that the people on the board and the people in IT can talk about the risks and people on the board can ask challenging questions of their teams.”
Corporate leaders need to “understand cyber-risk in the same way they understand financial risk or health and safety risk,” he added.
Board oversight
The shift of responsibility for cybersecurity oversight to boards is becoming increasingly clear. At the same conference, Matthew Fell, chief UK policy director of the CBI, said that as cyber-threats pose one of the biggest risks to a company’s finances and reputation, companies needed to recognise that digital security was no longer the sole responsibility of the IT team.
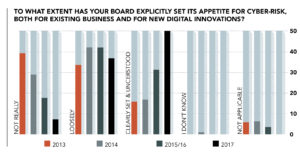
Given the barrage of cyber-attacks and the ensuing impact of disrupted business operations, financial, legal and regulatory risks, a thorough approach to putting in place robust protection and tackling breaches efficiently is vital. But just what is the state of boardroom oversight on cybersecurity?
Despite the urgency and gravity of threats, board management of cyber-risks remains patchy and is not always at the top of the agenda.
The UK government’s FTSE 350 report, Cyber Governance Health Check 2017, showed that just 54% of boards view cybersecurity as a top risk compared with other risks. More than two-thirds (68%) had no training to deal with a cyber-incident, while 57% claimed a clear understanding of potential impacts of a loss or disruption of data. The statistics are sobering.
Investors are also looking to boards for oversight. “Investors increasingly expect cybersecurity issues to fall within the remit of company boards and their sub-committees, given the potential physical and economic implications of a cybersecurity incident on business operations,” says Fiona Reynolds, CEO of the Principles for Responsible Investment (PRI), whose global signatories represent $80trn of assets under management.
So, what do boards need to do to be in control?
There is no shortage of guidance from institutions and governments on how to tackle the problem. The NCSC has published advice to help boards better understand and prepare themselves to deal with cybersecurity issues. The Bank of England, the Financial Conduct Authority and TheCityUK also provide guidelines on how boards of financial companies can tighten cybersecurity resilience.
Cybersecurity experts advise boards to make sure that clear policies and procedures are in place to tackle cybercrime and protect personal data. A good starting point is to ensure that all members have a clear understanding of the basics of cybersecurity and how the company can be affected by different types of cyber-attacks. Management and the chief IT officer need to explain clearly to the board, in non-technical language, the protection systems in place and vulnerability levels.
Gaining the right information is a two-way exercise and directors, particularly non-executives, who are not involved in the day-to-day running of the business, must ask tough questions to get a clear picture.
“It is the board’s job to ask the right questions and get the right answers from management about the company’s cybersecurity position,” says Peter Swabey, head of policy and research at ICSA: the Governance Institute.
Questions from the board should include how the company will withstand a range of cyber-attacks, existing cyberprotection measures, identifying weak spots, and asking what is being done to mitigate risks. Quality, comprehensive information is needed for the board to assess the situation.
Directors are often deterred from asking questions by IT specialists who say it is too complicated to explain, but boards must push back to get clear, up-to-date information. This may seem obvious, yet less than a third of boards surveyed in the FTSE 350 Cyber Governance report said they received comprehensive information.
Systems and procedures
What systems and procedures should be in place, then? Savvy boards will insist that “management clearly explain the cybersecurity system in place, what it does and why it is a better system than others,” says Swabey. This step is essential for executive and non-executive members to review and evaluate management approaches to cybersecurity strategy, policy and procedure.
Making sure that management tests the systems and procedures through regular crisis runs is another important task for boards. If there is doubt about effectiveness, then external expertise should be brought in. It is up to senior management to convince the board that the protection measures and response plan are sufficiently resilient. It is also essential for the board’s overview to receive internal audit reports on the state of cybersecurity.
“The ultimate decisions on whether the cybersecurity framework, policy and procedure are robust enough lies with the board,” says Swabey. As part of its oversight role, the board must also decide whether the level of risk is in line with the risk appetite of the business.
Many boards, particularly those of larger companies, appoint a non-executive director with cybersecurity experience or technology skills. This can be helpful for members, including the chair, to gain a better understanding and oversight of the risks involved. The trend is changing the traditional mix of board recruitment and pushes search executives to broaden their talent pool to draw in suitable candidates.
As the cybersecurity threat rises, there is some evidence that boards are spending more money on resources and infrastructure in order to boost awareness and defences. According to the summer Boardroom Bellwether survey, by ICSA and the Financial Times, 88% of FTSE 350 companies said their boards were increasing spending to mitigate cyber-risk.
New data protection rules, the General Data Protection Regulation (GDPR), which came into force in May, are reforming the way companies collect, use and store personal data. The aim is to make sure companies are protecting the personal data of EU citizens by managing security risk and minimising the impact of breaches when they occur.
The GDPR provides clear guidelines for companies that are breached, and boards must have a clear post-breach plan of action in place. Reporting the breach to regulators and stakeholders within 72 hours of discovery is essential, as failure to do this can result in big fines.
The task of overseeing good, timely communication on the state of cybersecurity also falls to the board and includes ensuring good standards of corporate reporting. Poor disclosure on cybersecurity in corporate reporting often prevents investors from assessing a company’s vulnerability to breaches.
—Fiona Reynolds, PRI
Recent research carried out by the PRI, which studied 100 global companies on aspects of cybersecurity management, showed that nearly 60% did not indicate that their board or its sub-committees were responsible for cybersecurity-related issues. Almost two-thirds of companies provided little or no information about the frequency and channels of communication to the board.
“Although companies are increasingly recognising cyber-risks and their impacts, corporate information in the public domain does not reassure investors that companies have adequate governance structures and measures in place to deal with cybersecurity challenges,” says Reynolds.
This is a problem because “the lack of disclosure makes it difficult for investors to differentiate between those companies that are proactively developing, monitoring and managing cyber-risks versus those failing to prioritise these risks,” she adds. Reynolds’ comments come as the PRI steps up its engagement on cybersecurity with boards and management.
Keeping up
The route to becoming a board with good cybersecurity oversight is not without difficulties. One obstacle hindering progress is the “it won’t happen to us” mentality, which can result in members brushing the problem aside. The danger of groupthink on the issue can lead to cybersecurity not being at the top of the board agenda or, in some cases, not on it at all.
Keeping up with the speed of fast-changing cyber-attacks is also difficult as cyber-criminals continue to invent new attack methods. Many boards have already increased the amount of time they spend in the boardroom and find it difficult to chase management and the CIO for regular cyber-updates.
Investment costs in resources—from infrastructure to expertise and compliance with new regulation—can also be heavy, particularly for small companies. However, boards are beginning to realise that the steep cost of data losses and the ensuing damage to operations and reputation is even bigger.
Effective board oversight of cybersecurity is still a work in progress, with “some doing more than others,” says Swabey. The task is enormous but signs of directors attempting to safeguard information assets are emerging.
—Ciaran Martin, NCSC
“Business boards are stepping up to the challenge of improving their cyber-literacy but firms recognise more progress is needed,” says the CBI’s Matthew Fell. It is, at least, a step in the direction of strengthening cyber-defences, according to the NCSC’s Ciaran Martin, who had this to say in his speech to the CBI in September last year:
“There are three misconceptions we often come across. The first: that ‘cyber is too complex so I won’t understand it’. The second: that ‘cyber is sophisticated so I can’t do anything to stop it’. And the third: that ‘cyber is targeted so I’m not at risk’. None of these are really true and these misconceptions are damaging. You can’t manage risk you don’t understand. So we need to demystify the topic.
“At board level, this means closing the knowledge gap between the board and the technical team. That’s why it means board members becoming a little bit technical. So that the people on the board and the people in IT can talk about the risks, and people on the board can ask challenging questions of their teams. You don’t need to know everything. Just enough to make your own defences stronger.
“No-one in government is asking you to be able to take on the best hostile nation state on a good day on your own. No-one in government is asking you to make cybersecurity your top priority. Your core business is your top priority. We do expect you, however, to be good enough at cybersecurity to take care of the things you care about. And that means you have to understand what they are, and what you can do to protect yourselves.”